
By identifying vulnerabilities, VulnSign is help information security teams protect against cyber threats such as OWASP top vulnerabilities.
VulnSign is regularly scan systems and applications for new vulnerabilities, helping teams to stay up-to-date on the security of their systems.
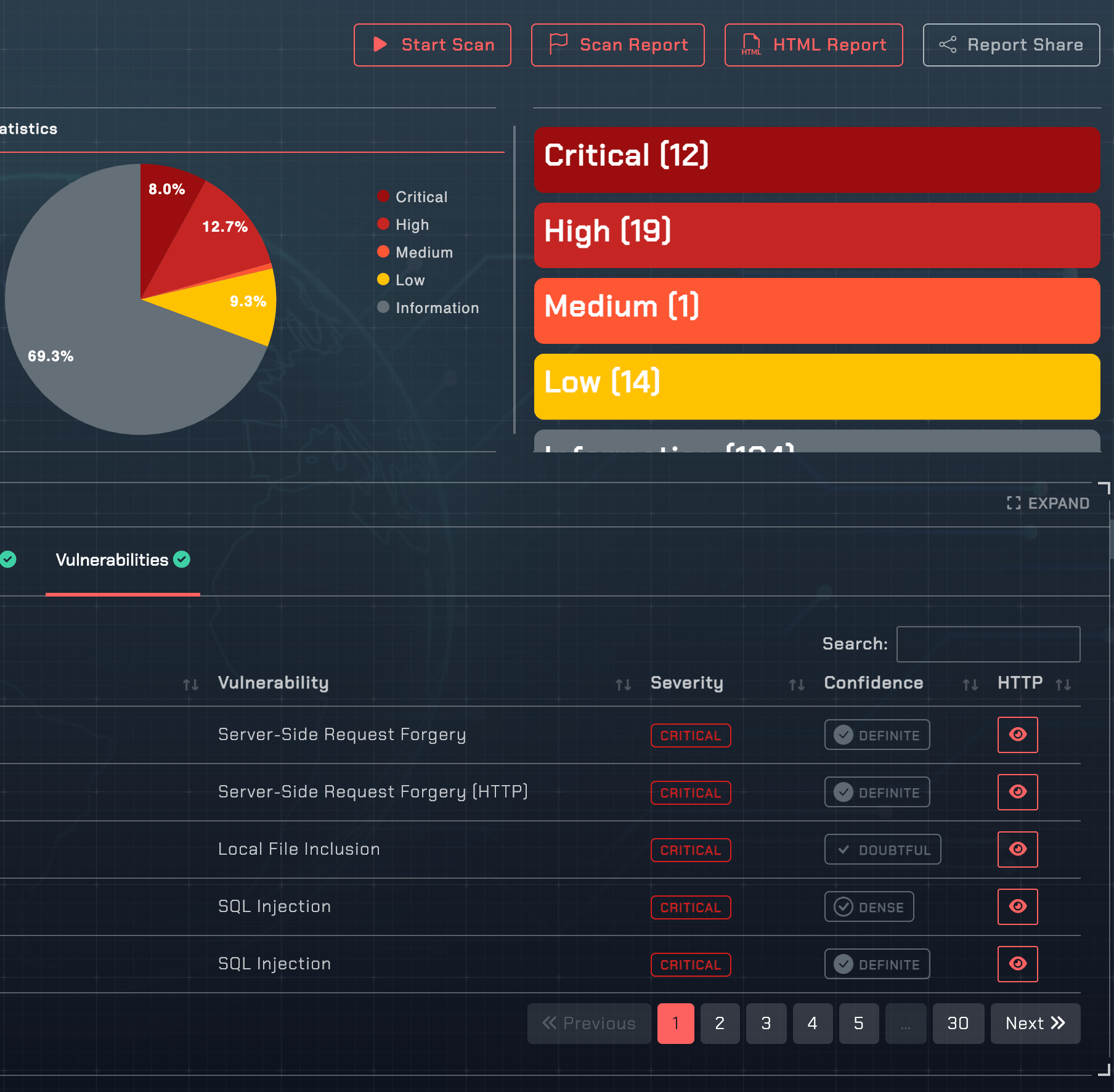
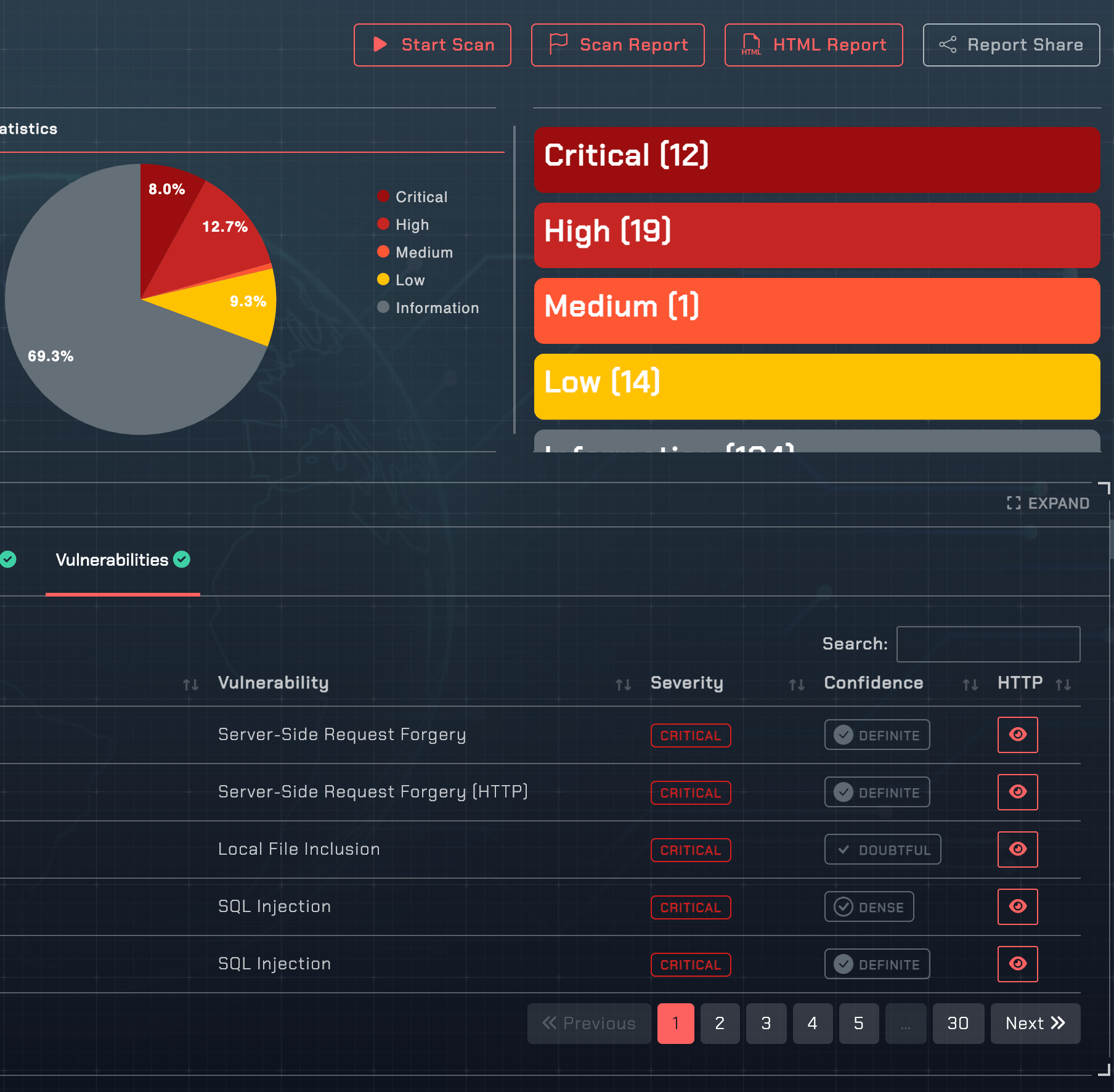
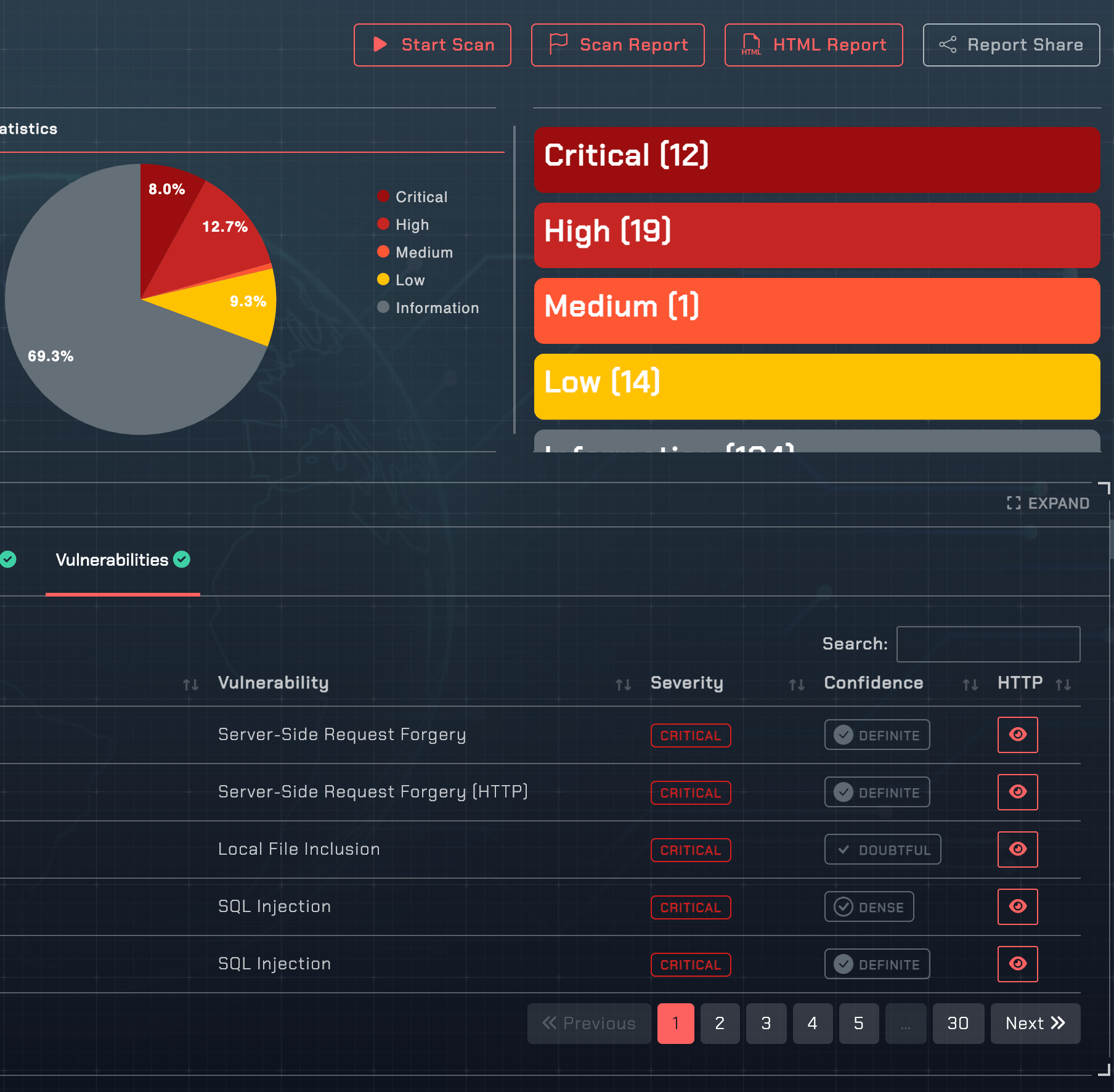
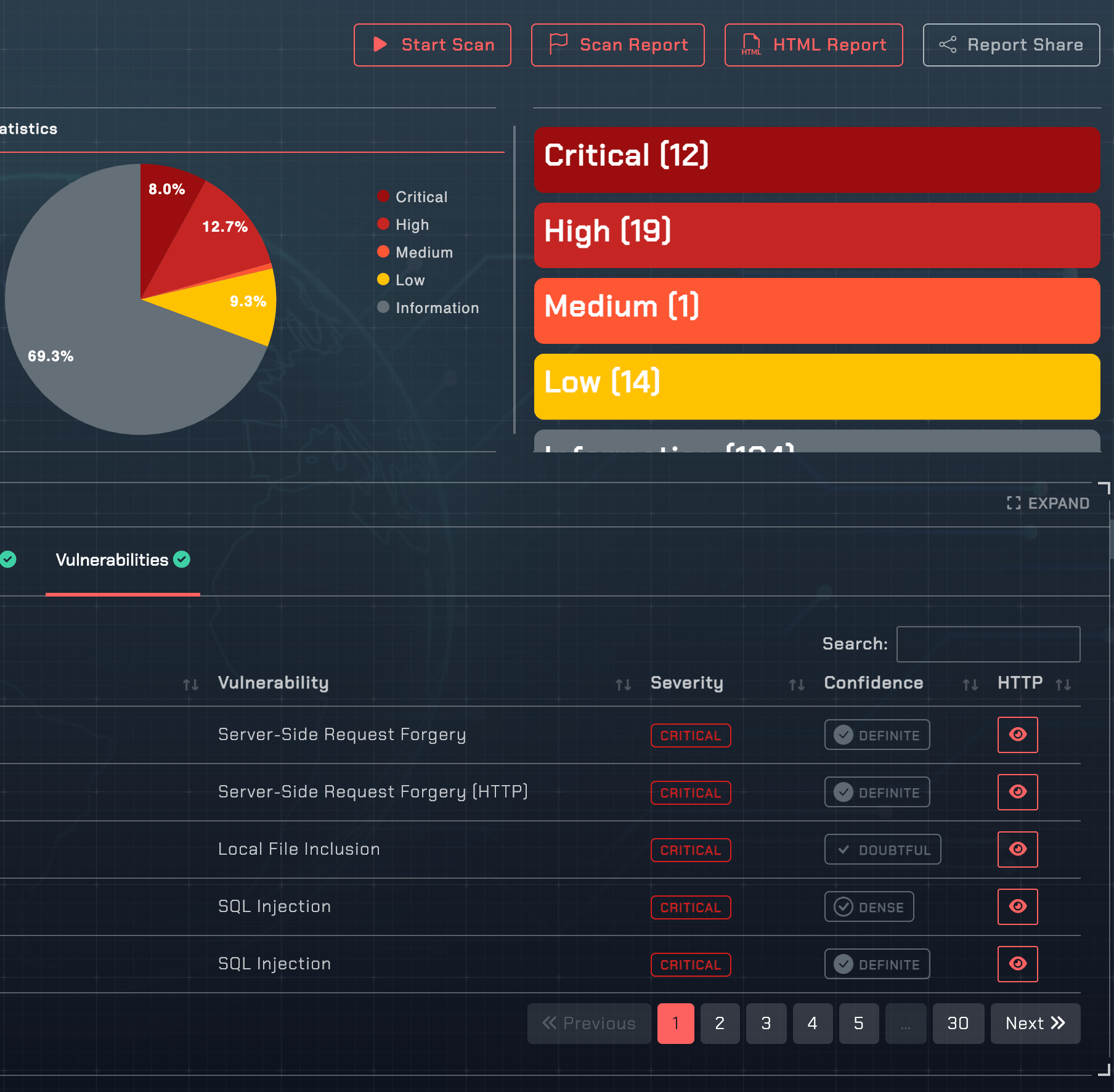
VulSign is prioritize vulnerabilities based on their severity, helping teams to focus their efforts on the most critical issues first.
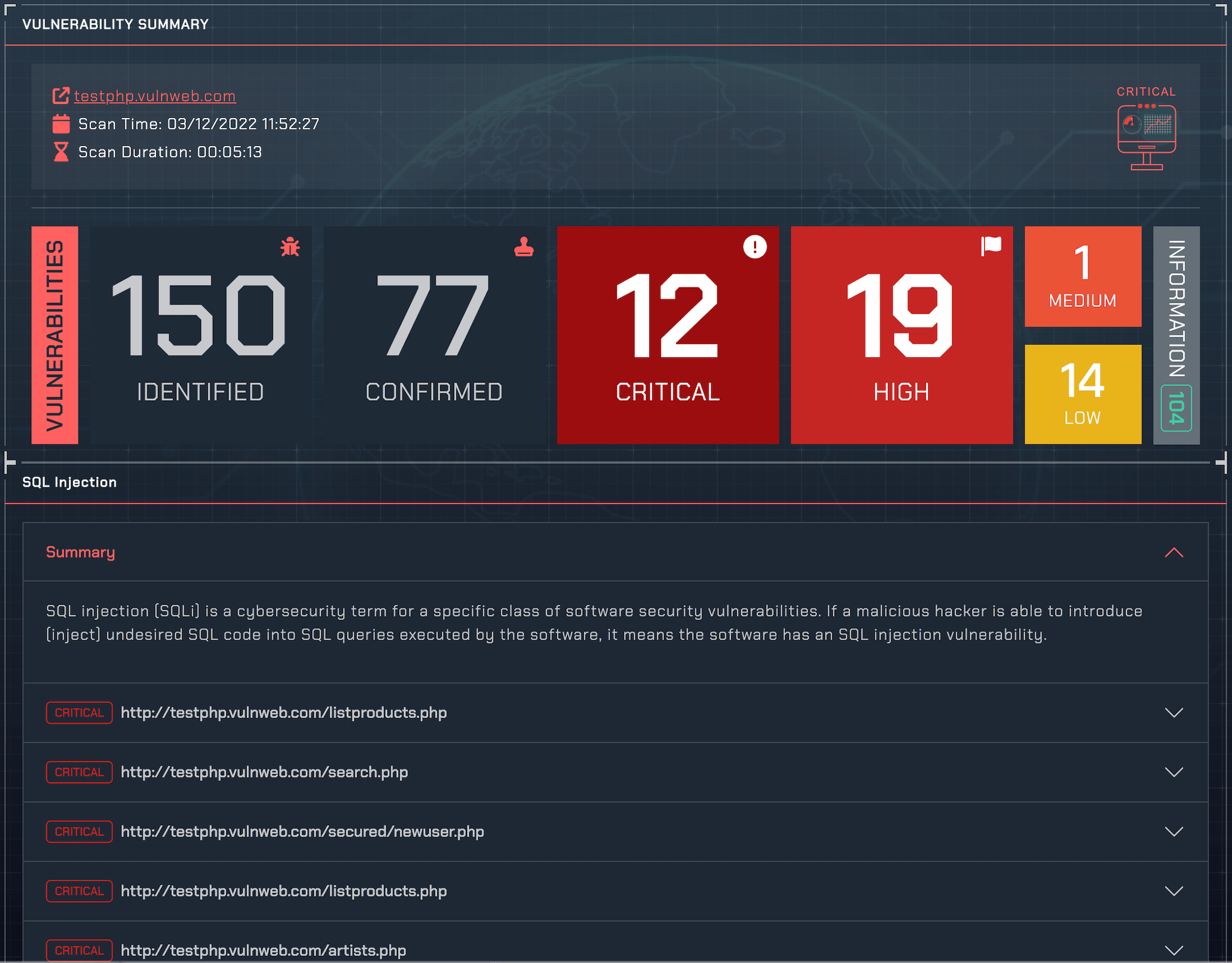
VulnSign's ability to generate proof of exploit for every vulnerability it discovers makes it easy for devs to reproduce the bug and identify remedy.
VulnSign is a highly respected and widely used tool for identifying vulnerabilities in web applications.
It is trusted by top companies and organizations across a variety of industries.
VulnSign is a DAST application designed to meet the needs of every important role in the IT.
Information security is an important concern for a Chief Technology Officer (CTO) because it is essential for protecting an organization's data and systems from unauthorized access, use, disclosure, disruption, modification, or destruction. This is particularly important in today's digital age, where data is often the most valuable asset of a business.
There are many potential threats to information security, such as hacking, phishing, malware, and ransomware attacks. These threats can have serious consequences for an organization, including financial losses, damage to reputation, and legal liabilities.
As a CTO, it is important to have a strong understanding of information security and to take steps to protect the organization's data and systems.
VulnSign is a comprehensive web application security solution designed to meet the needs of security teams. It offers scalable, multi-user capabilities and includes built-in workflow and reporting tools. It can also be easily integrated into any development or testing environment.
As an engineering manager, it is important to understand the importance of information security and to prioritize it within your team and organization. In today's digital age, data is often the most valuable asset of a business, and a breach of security can have serious consequences, including financial losses, damage to reputation, and legal liabilities.
As an engineering manager, it is your responsibility to ensure that the systems and applications developed by your team are secure and that appropriate security protocols and practices are in place. This may involve implementing security policies, training team members on security best practices, and regularly testing and updating the organization's security systems.
It is also important to stay up-to-date on the latest threats and technologies in the field, as the landscape of information security is constantly evolving. By prioritizing information security, you can help protect the organization and its assets, and build trust with customers and stakeholders.
Developers can use VulnSign DAST to regularly scan their applications or sites and fix any vulnerabilities that are found. This can help make the applications or sites more secure against malicious attacks and prevent serious consequences such as data loss. In addition, these scans can provide more information about the security of the application or site and help take more effective security measures.
VulnSign's ability to generate proof of exploit for every confirmed vulnerability it discovers makes it easy for engineers to reproduce the bug and quickly identify a solution. This saves time that would otherwise be wasted on attempting to fix issues that do not actually need to be addressed. Overall, this technology helps engineers more efficiently and effectively address vulnerabilities in their systems.
Transform your DevOps practices into DevSecOps by adding a few steps to your workflow. Continuously check your web applications and APIs for vulnerabilities before releasing to production, ensuring that your next release is secure.
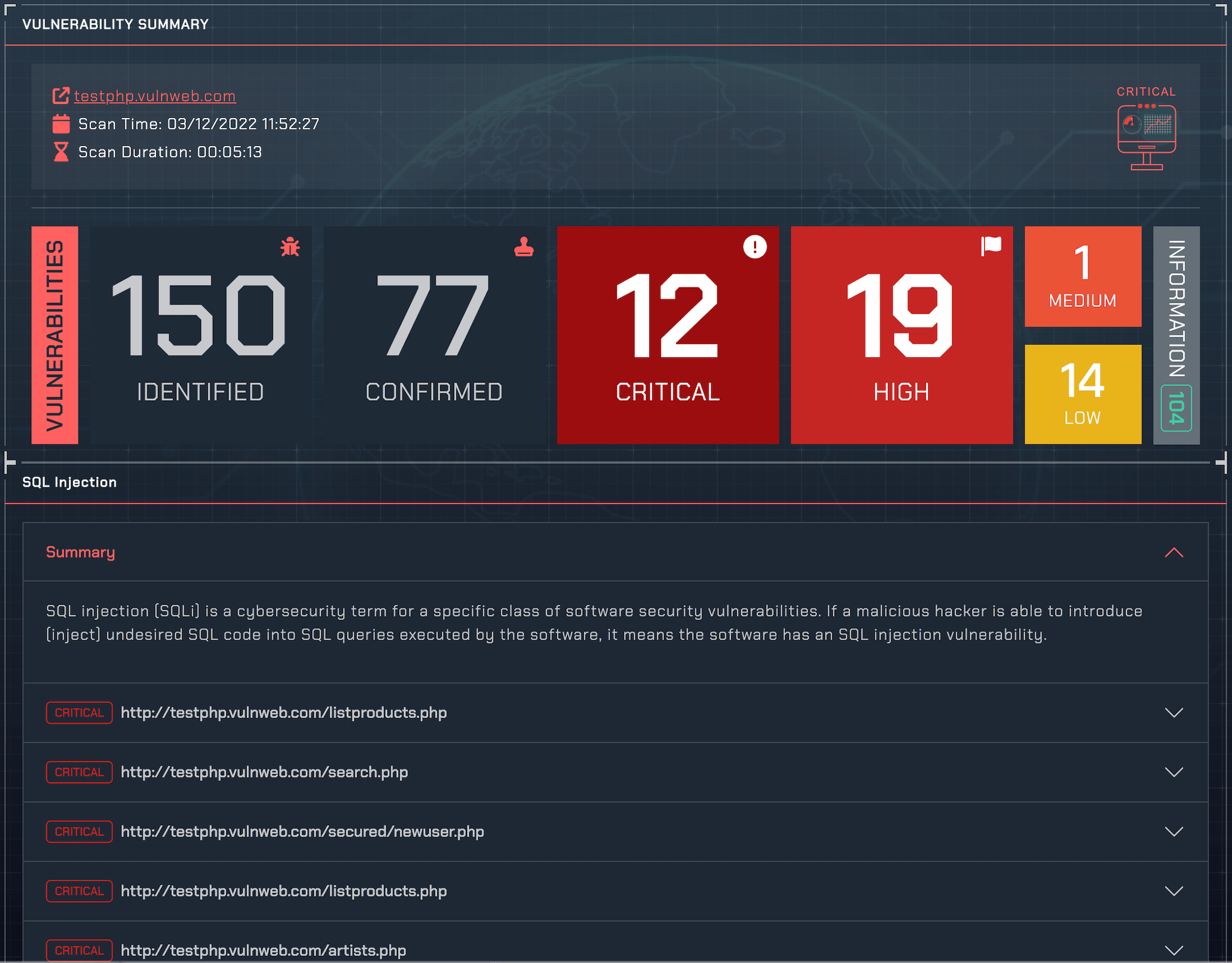
False positives can be a significant issue for vulnerability scanners. VulnSign's Proof-Based Scanning system helps to eliminate this problem by verifying potential vulnerabilities, which reduces the amount of manual work that your team needs to do. By integrating VulnSign into your CI/CD workflows, you can avoid disruptions caused by false positives, allowing your team to focus on more important tasks.